Why xorkee for authentication?
The digital world is rife with security risks you shouldn't have to live with. Conventional security measures have reached their breaking point owing to the strides AI has made. One-Time Passwords (OTPs) are frequently compromised via side-channel attacks and SIM swaps, while biometrics offer weak remote verification.
xorkee authentication overcomes these limitations by offering a secure, authentication solution that protects you and your clients from internet threats. It simplifies public key authentication where users approve transactions with strong cryptographic identities.
 offers
offers

The End of Stealable Credentials
Attackers thrive on stealing authentication factors like your passwords and OTPs. We eliminated that possibility. The xorkee authentication identity relies on cryptographic keys that are non-exportable. They are generated within your device's secure hardware environment or a token and are fundamentally bound to that physical device.

Evidence for transactions
OTP is a fleeting evidence which contains no context of what was approved and who approved it. xorkee authentication on the other hand relies on cryptographic attestation that binds the user’s identity to specific terms of transaction, enabling undeniable record of consent.

One Identity, Unlimited services
Daily interactions with dozens of services cause fatigue from unique passwords/devices/IDs. xorkee authentication offers one identity for all, with separate secure spaces per service and streamlines life securely.

Minimal maintenance overhead
Credential management and device changes are handled by the xorkee infrastructure, and the user procures the crypto token by himself allowing the service providers using xorkee authentication to attend only to the processes relevant to their service.

The wonder of public key authentication
xorkee authentication does not store any sensitive credentials of users like passwords, OTP , biometrics - nothing a hacker will benefit from and nothing that will be harmful to the service providers or the users if exposed.

Respects user dignity
We eliminate the need and the temptation to study the user environment, habits, contacts, activities or geographic location to arrive at the probability that he is the right user. xorkee authentication works on the certainty that if it is his key and his signature, it is him.
Simple End User Experience
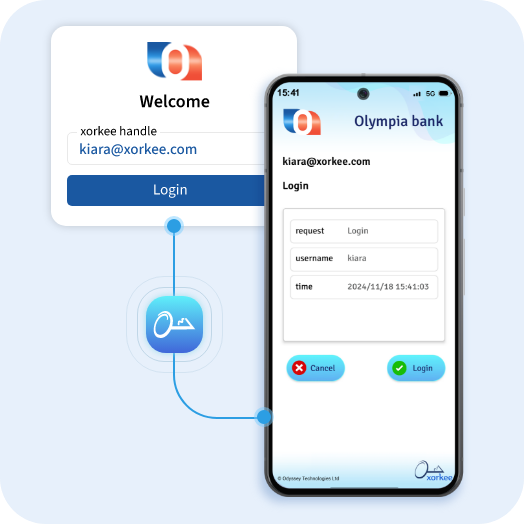
User installs xorkee application on his device and registers a unique xorkee handle.
The user enrolls the handle with a business application.
When the user wants to login or authenticate any transaction, a request is initiated for authentication as a push notification.
The user’s xorkee app presents the notification for approval. The user then approves with a token password/ fingerprint/ face id/ PIN.
Deployment Options
xorkeeauth is available both as a SaaS as well as an on-premises product.


Otherwise the xorkee based Snorkel-TX and xorkeeauth behave identically from the point of the application as well as the end users.